What is Tails?
Tails stands for ‘the amnesic incognito live system’ and is a full blown operating system built on the Debian version of Linux.
Installed on a USB stick or SD card, you can boot the OS on just about any computer and it protects your privacy and renders you anonymous on the web.
It does this by forcing all internet connections through the Tor network and by leaving no trace of any activity on the host computer (unless you explicitly set it to).
Not only that but you also get tools to encrypt your files, emails and instant messages.
The installation of Tails is a bit fiddly but once installed you will find all the features of Linux Debian plus the following privacy extras:-
- The Tor Browser – a pre-configured web browser to protect your anonymity using Startpage as it’s default search engine. By default the browser sets ‘do not track’ preferences and does not remember browsing history. Also includes the Add-ons Adblock Plus, HTTPS-Everywhere and NoScript.
- Claws Mail – encrypted email with a lightweight and fast GTK+ mail client.
- Pidgin Instant Messenger – encrypted chat over IM, supporting AIM, Google Talk, Jabber/XMPP, MSN, Yahoo and more.
- KeePassX – a cross platform password manager.
- OpenPGP Encryption – manipulate text using OpenPGP. Encrypt text in your browser, before sending it by email for example.
As part of the Linux Debian install you get:-
- LibreOffice – a full office suite including word processor, spreadsheet, draw, presentation and document viewer.
- Sound and video players, graphic editors, accessories and tools, more…
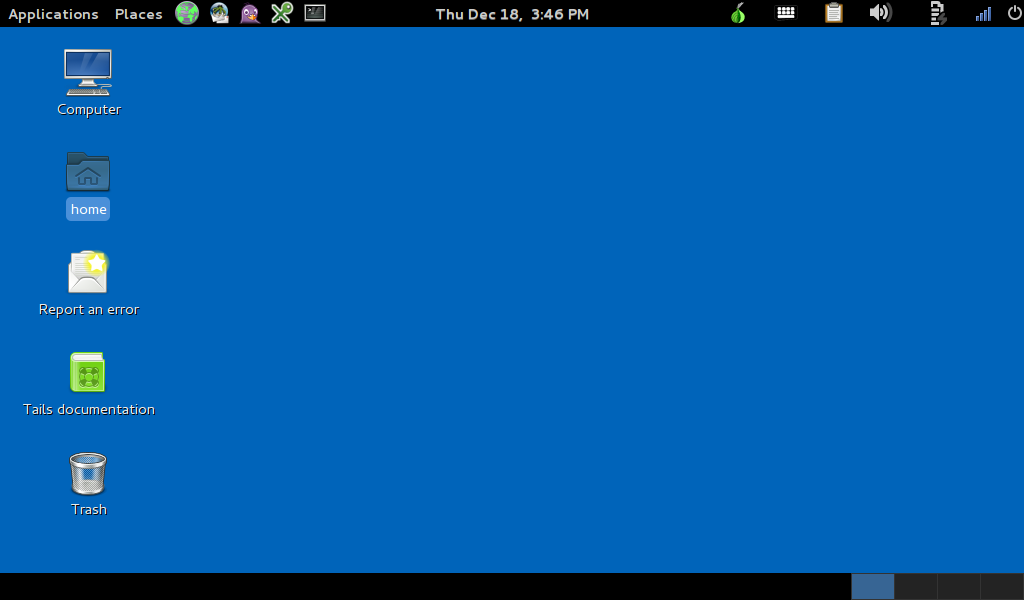
The Tails desktop…
Amnesic
You can use Tails on any computer regardless of the operating system installed on it. You can use it in the same way on your computer or any other and after shutting down Tails, the computer simply starts again using its usual operating system.
Tails does not use the computer’s hard-disks and only stores temporarily in RAM which is automatically erased when the computer shuts down. You can still explicitly save stuff to a USB or external hard-disk of course.
Use the persistent volume
But beware, by default Tails literally does forget everything. Create a document and save it to your desktop (or any other directory) and it won’t be there the next time you boot up. Likewise, it won’t remember your network connections and passwords, your mail and messaging profiles, printer set-ups, etc.
However, you can easily remedy this by creating a persistent volume on the USB stick or SD card on which you have installed Tails.
This means you don’t have to keep adding your ISP password every time you use it and you can access all documents, etc. you create from any computer you boot up from. But beware using the persistent volume can lessen your security and anonymity.
Pros and Cons
It’s free! What could be better than that!? And it’s probably as close as you can get to ‘privacy on a stick’ at the moment.
Once installed you can just fire it up, cruise the web anonymously and enjoy the benefits of encrypted emails , messaging and documents.
If you are already familiar with Linux, what’s not to like? The Debian version is pretty slick and includes a stack of applications, accessories and tools.
However, if you don’t like Linux for any reason you are not going to like Tails. It’s very fiddly to install and if you’re not even remotely a geek you should probably steer clear.
Also, being forced to use the Tor network may not suit everyone. Tor can be slow and is unsuitable for P2P downloading or streaming geo-restricted media content. (See our more detailed analysis of using the Tor network).
It’s important to understand that whilst Tails is a good tool to protect your privacy while using it on a computer, it’s not infallible and understanding its limits is important before deciding if it’s right for you.
Use the Latest Version
Beware! You should always use the latest version of the Tails software as each release includes security fixes as well any improvements and enhancements.
Please add your comments below or in the related discussion topic of our forum.